Ryan Petrich, a well-known Dev known for his tweaks such as Activator, Display Recorder, RetinaPad and Action Menu (among other things) has released a major security fix for the now-infamous "SSL Bug" on devices running iOS 6.0-6.1.5 as well as iOS 7.0-7.0.5. In case you live under a rock or something, let it be known that this is a MAJOR security flaw. It affects everything from Safari to Mail to potentially your favorite online banking app. For details on the security flaw, go here, here, here and here.
Now obviously, the "easiest" way to fix this major flaw would be to update to iOS 7.0.6 either through OTA (Settings - General - Software Update) or through iTunes. Those of you still sporting the iPhone 3GS or in possession of the iPod Touch 4th Generation, you will need to update to iOS 6.1.6, the latest version of Apple's operating system available for these devices. However, if you are jaibroken, chances are you know that things aren't as simple as an OTA update or an iTunes update. Being jailbroken means that you must restore through iTunes to the latest version available, effectively performing a clean install. Then you must re-jailbreak (that is, if you're still into jailbreaking.) Then there's the task of making sure your tweaks are still compatible with the latest version of iOS. This can take hours. Not to mention if you have multiple jailbroken iDevices.
I currently have an iPad 2 running iOS 5.1.1 jailbroken, and an iPhone 4S running iOS 6.1 jailbroken. I haven't had the time to update just yet. Meanwhile since the news broke about the major security flaw, I immediately stopped doing anything that normally relies on a working SSL layer for security. So I stopped doing pretty much everything except browsing the web on my iDevices until I could find the time to update.
Luckily, a fix has arrived as a stop-gap measure until I find the time to update (I better get moving, the iOS 7 jailbreak could be closed any time now!)
Now for the goods:
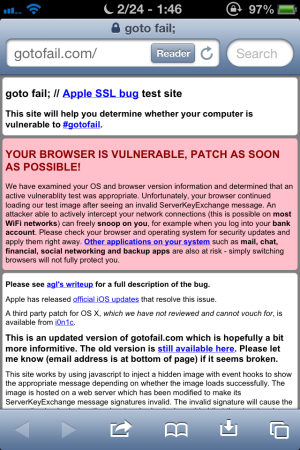
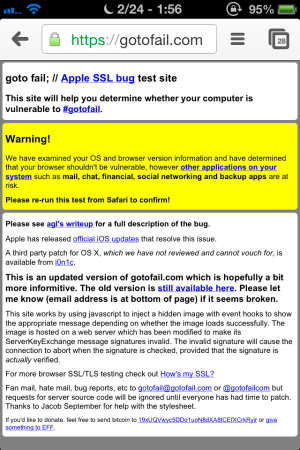
First I went to http://gotofail.com/ in Safari on my iPhone to check for the flaw. Sure enough, there it was!

Then I tried in Chrome. Looks like Chrome isn't vulnerable, even unpatched. That's good, but that doesn't mean squat when virtually every other app you use is potentially vulnerable!
Alright, so now that we know we're vulnerable, now what? Well, if you are jailbroken and don't want to go through the hassle of updating just yet, here is a temporary solution:
Start off by opening Cydia.

On the bottom menu tap Manage, then tap Sources (on iPad, simply tap Sources on the bottom menu.) Now tap Edit in the top-right corner, then tap Add in the top-left corner.

You should come up with a screen like the above. Type in "http://rpetri.ch/repo/" (without quotes) then tap Add Source.
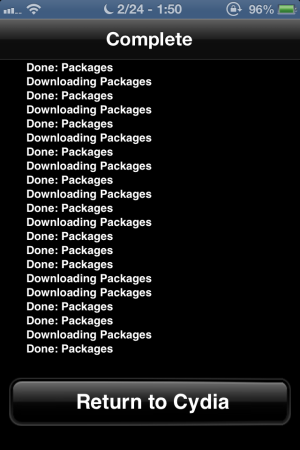
Let Cydia do it's thing, then tap Return to Cydia when it finishes.

Now tap Search in the bottom menu and type in SSLPatch (or tap the suggestion when it comes up and save a few taps.)
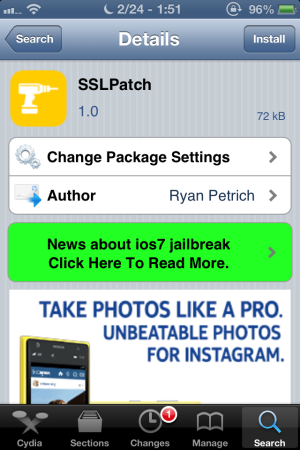
You should now be on a page similar to this one. Tap Install in the top-right corner then tap Confirm.

Once again let Cydia do it's thing, then tap Reboot Device when it's finished. NOTE: It may say Restart Springboard instead of Reboot Device. If so, tap Restart Springboard.
DONE!! Takes all of five minutes.

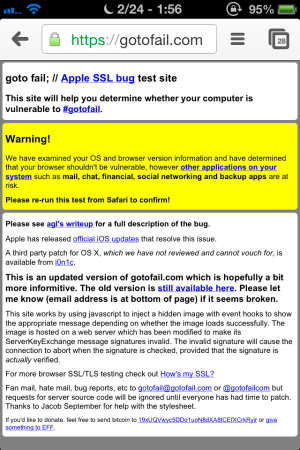
Now you can open Safari again and go to http://gotofail.com/ and confirm that this nasty bug has been squished. Looks like it worked for me!
Just for grins, I went back to that site again in Chrome, post-fix, just to see what it would say. It says pretty much the same thing it said before.
Now, for the most part, with this patch installed you are temporarily safe. I say that because there are a couple caveats with this fix. This fix does not work in Safe Mode, so if your springboard crashes to safe mode, get out of safe mode ASAP (the latest version of iOS does not have this issue.) I'm still on iOS 6.1 (for now) and it's pretty obvious when you're in Safe Mode, with the popup and the Safe Mode label in the status bar. I thought I read somewhere that Safe Mode isn't near as obvious on iOS 7, that all it changes is the wallpaper or some such. Perhaps that's been updated, I don't know. Feel free to correct me if I'm wrong. If it's still not obvious, one could inadvertently do things thinking that they're secure when they're not because they're in Safe Mode. The other thing is that tweaks/apps that run as root will still have the vulnerability. Two examples would be Cydia and iFile. So you may want to hold off on purchasing apps through Cydia until you can update to the latest version of iOS. If you plan on upgrading to iOS 7, and also plan on jailbreaking, I strongly suggest doing so ASAP, as time is running out for the jailbreak.
Another thing that I noticed is that out of the three sites I used to check my SSL, http://howsmyssl.com/ still failed in Safari on the iPhone running 6.1 even with the patch. However, https://www.imperialviolet.org:1266/ did not load which means it passed. Then of course, http://gotofail.com/ also passed. So I'm not sure what's going on there. As per usual, Chrome passes everything.
The iPad 2 running 5.1.1 also passes everything in Safari, without the need for this patch. So those of you with an iPad 1 or an iPod Touch 3rd Generation, it sucks being stuck on 5.1.1 but at least it's safe (for now.) If you own anything older than the iPod touch 3rd Generation or the iPhone 3GS, well first of all I would like to congratulate you on holding out for so long, I guess you could save a lot of money by keeping a device for 5-6 years straight. It looks like this flaw was introduced in iOS 6 (almost 1.5 years ago!!) so your older devices running those old iOS versions are probably fine.
So there you have it. Stay safe people!
Now obviously, the "easiest" way to fix this major flaw would be to update to iOS 7.0.6 either through OTA (Settings - General - Software Update) or through iTunes. Those of you still sporting the iPhone 3GS or in possession of the iPod Touch 4th Generation, you will need to update to iOS 6.1.6, the latest version of Apple's operating system available for these devices. However, if you are jaibroken, chances are you know that things aren't as simple as an OTA update or an iTunes update. Being jailbroken means that you must restore through iTunes to the latest version available, effectively performing a clean install. Then you must re-jailbreak (that is, if you're still into jailbreaking.) Then there's the task of making sure your tweaks are still compatible with the latest version of iOS. This can take hours. Not to mention if you have multiple jailbroken iDevices.
I currently have an iPad 2 running iOS 5.1.1 jailbroken, and an iPhone 4S running iOS 6.1 jailbroken. I haven't had the time to update just yet. Meanwhile since the news broke about the major security flaw, I immediately stopped doing anything that normally relies on a working SSL layer for security. So I stopped doing pretty much everything except browsing the web on my iDevices until I could find the time to update.
Luckily, a fix has arrived as a stop-gap measure until I find the time to update (I better get moving, the iOS 7 jailbreak could be closed any time now!)
Now for the goods:
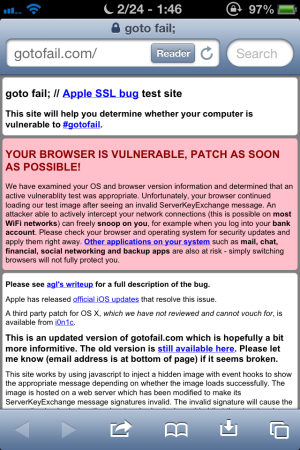
First I went to http://gotofail.com/ in Safari on my iPhone to check for the flaw. Sure enough, there it was!

Then I tried in Chrome. Looks like Chrome isn't vulnerable, even unpatched. That's good, but that doesn't mean squat when virtually every other app you use is potentially vulnerable!
Alright, so now that we know we're vulnerable, now what? Well, if you are jailbroken and don't want to go through the hassle of updating just yet, here is a temporary solution:
Start off by opening Cydia.

On the bottom menu tap Manage, then tap Sources (on iPad, simply tap Sources on the bottom menu.) Now tap Edit in the top-right corner, then tap Add in the top-left corner.

You should come up with a screen like the above. Type in "http://rpetri.ch/repo/" (without quotes) then tap Add Source.
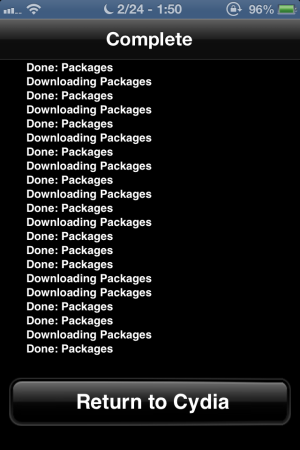
Let Cydia do it's thing, then tap Return to Cydia when it finishes.

Now tap Search in the bottom menu and type in SSLPatch (or tap the suggestion when it comes up and save a few taps.)
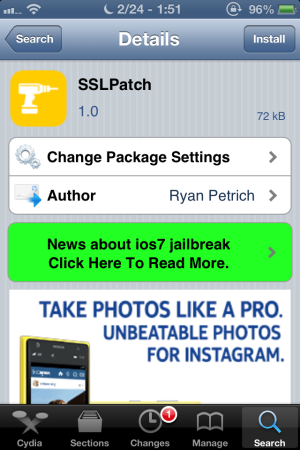
You should now be on a page similar to this one. Tap Install in the top-right corner then tap Confirm.

Once again let Cydia do it's thing, then tap Reboot Device when it's finished. NOTE: It may say Restart Springboard instead of Reboot Device. If so, tap Restart Springboard.
DONE!! Takes all of five minutes.

Now you can open Safari again and go to http://gotofail.com/ and confirm that this nasty bug has been squished. Looks like it worked for me!
Just for grins, I went back to that site again in Chrome, post-fix, just to see what it would say. It says pretty much the same thing it said before.
Now, for the most part, with this patch installed you are temporarily safe. I say that because there are a couple caveats with this fix. This fix does not work in Safe Mode, so if your springboard crashes to safe mode, get out of safe mode ASAP (the latest version of iOS does not have this issue.) I'm still on iOS 6.1 (for now) and it's pretty obvious when you're in Safe Mode, with the popup and the Safe Mode label in the status bar. I thought I read somewhere that Safe Mode isn't near as obvious on iOS 7, that all it changes is the wallpaper or some such. Perhaps that's been updated, I don't know. Feel free to correct me if I'm wrong. If it's still not obvious, one could inadvertently do things thinking that they're secure when they're not because they're in Safe Mode. The other thing is that tweaks/apps that run as root will still have the vulnerability. Two examples would be Cydia and iFile. So you may want to hold off on purchasing apps through Cydia until you can update to the latest version of iOS. If you plan on upgrading to iOS 7, and also plan on jailbreaking, I strongly suggest doing so ASAP, as time is running out for the jailbreak.
Another thing that I noticed is that out of the three sites I used to check my SSL, http://howsmyssl.com/ still failed in Safari on the iPhone running 6.1 even with the patch. However, https://www.imperialviolet.org:1266/ did not load which means it passed. Then of course, http://gotofail.com/ also passed. So I'm not sure what's going on there. As per usual, Chrome passes everything.
The iPad 2 running 5.1.1 also passes everything in Safari, without the need for this patch. So those of you with an iPad 1 or an iPod Touch 3rd Generation, it sucks being stuck on 5.1.1 but at least it's safe (for now.) If you own anything older than the iPod touch 3rd Generation or the iPhone 3GS, well first of all I would like to congratulate you on holding out for so long, I guess you could save a lot of money by keeping a device for 5-6 years straight. It looks like this flaw was introduced in iOS 6 (almost 1.5 years ago!!) so your older devices running those old iOS versions are probably fine.
So there you have it. Stay safe people!